Amazon Web Services (AWS) enables organizations to build and scale applications quickly and securely. However, continuously adding new tools and services introduces new security challenges. According to reports, 70 percent of enterprise IT leaders are concerned about how secure they are in the cloud and 61 percent of small- to medium-sized businesses (SMBs) believe their cloud data is at risk.
AWS provides many different security tools to help customers keep their AWS accounts and applications secure. In fact, there was significant focus on AWS security best practices at re:Invent 2020. See the Best practices with Amazon S3 recap and Jeremy Cowan’s Securing your Amazon EKS applications: Best practices session for some of the details.
In this article, we’ll review the top ten AWS security tools you should consider using to improve your security posture in 2021 and beyond. Before we do that, we will briefly explain AWS account security versus application and service security. Organizations must focus on keeping both secure to protect against different types of attacks.
Account Security Versus Application And Service Security
AWS provides security tools designed to improve both account security and application and service security.
An AWS account is an attack vector, as resources and data are accessible through the public application programming interface (API). Implementing a secure identity and access management strategy helps prevent leaking data — such as in S3 buckets — to the public. AWS’s many tools provide insights into your configured permissions and access patterns, and record all actions for compliance and audit purposes.
Applications and services hosted in AWS are susceptible to different kinds of threats from the outside. Cross-site scripting (XSS), SQL injection, and brute-force attacks target public endpoints. Distributed denial-of-service (DDoS) attacks may attempt to bring down your services, potentially compromising your architecture security. Without proper management, sensitive information — such as database credentials — may leak.
Therefore, it’s critical that organizations migrating to the cloud focus on minimizing risk and improving their overall security posture by addressing both account security as well as application and service security. The following AWS services lock down your cloud security, helping keep your customer data and systems safe from attack.
Top 6 AWS Account Security Tools
1. AWS Identity and Access Management (IAM)
AWS Identity and Access Management (IAM) is a web service for securely controlling access to AWS resources. It enables you to create and control services for user authentication or limit access to a certain set of people who use your AWS resources.
The IAM workflow includes the following six elements:
- A principal is an entity that can perform actions on an AWS resource. A user, a role or an application can be a principal.
- Authentication is the process of confirming the identity of the principal trying to access an AWS product. The principal must provide its credentials or required keys for authentication.
- Request: A principal sends a request to AWS specifying the action and which resource should perform it.
- Authorization: By default, all resources are denied. IAM authorizes a request only if all parts of the request are allowed by a matching policy. After authenticating and authorizing the request, AWS approves the action.
- Actions are used to view, create, edit or delete a resource.
- Resources: A set of actions can be performed on a resource related to your AWS account.
Let us explore the components of IAM in the next section of the AWS IAM tutorial.
To review, here are some of the main features of IAM:
- Shared access to the AWS account. The main feature of IAM is that it allows you to create separate usernames and passwords for individual users or resources and delegate access.
- Granular permissions. Restrictions can be applied to requests. For example, you can allow the user to download information, but deny the user the ability to update information through the policies.
- Multifactor authentication (MFA). IAM supports MFA, in which users provide their username and password plus a one-time password from their phone—a randomly generated number used as an additional authentication factor.
- Identity Federation. If the user is already authenticated, such as through a Facebook or Google account, IAM can be made to trust that authentication method and then allow access based on it. This can also be used to allow users to maintain just one password for both on-premises and cloud environment work.
- Free to use. There is no additional charge for IAM security. There is no additional charge for creating additional users, groups or policies.
- PCI DSS compliance. The Payment Card Industry Data Security Standard is an information security standard for organizations that handle branded credit cards from the major card schemes. IAM complies with this standard.
- Password policy. The IAM password policy allows you to reset a password or rotate passwords remotely. You can also set rules, such as how a user should pick a password or how many attempts a user may make to provide a password before being denied access.
In the last section of the AWS IAM tutorial, let us go through a demo on how to create an S3 bucket using the multifactor authentication (MFA) feature.
2. Amazon GuardDuty
Amazon GuardDuty is a threat detection service that continuously monitors your AWS accounts and workloads for malicious activity and delivers detailed security findings for visibility and remediation. These include use of compromised credentials, simplified forensics and continuous monitoring of all security events seen in an AWS customers environment. With the announcement of new Malware Production, GuardDuty will scan EBS-backed EC2 instances with malicious behavior based on GuardDuty’s existing findings and report malware detected on EC2 and containers running on EC2 and instantly send data to Trellix Helix.
3. Amazon Macie
Amazon Macie is a security service that uses machine learning to automatically discover, classify and protect sensitive data in the Amazon Web Services (AWS) Cloud. It currently only supports Amazon Simple Storage Service (Amazon S3), but more AWS data stores are planned.
Macie can recognize any PII or Protected Health Information (PHI) that exists in your S3 buckets. Macie also monitors the S3 buckets themselves for security and access control. This all can help you meet regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) and General Data Privacy Regulation (GDPR) or just continually achieve the security you require in the AWS Cloud environment.
Within a few minutes after enabling Macie for your AWS account, Macie will generate your S3 bucket list in the region where you enabled it. Macie will also begin to monitor the security and access control of the buckets. When it detects the risk of unauthorized access or any accidental data leakage, it generates detailed findings.
The dashboard provides you with a summary that shows you how the data is accessed or moved. This dashboard gives you a view of the total number of buckets, the total number of objects, and the total number of S3 storage consumed.
It also breaks down S3 buckets by whether they are shared publicly, encrypted or not, and buckets shared inside and outside your AWS account or AWS Organization.
Create and run sensitive data discovery jobs to automatically discover, record, and report sensitive data in Amazon S3 buckets.
You can configure the job to run only once for on-demand analysis, or periodically for periodic analysis and monitoring.
A finding is a detailed report of potential policy violations for sensitive data in S3 buckets or S3 objects. Macie provides two types of findings: policy findings and sensitive data findings.
Macie can also send all findings to Amazon CloudWatch Events so you can build custom remediation and alert management.
4. AWS Config
AWS Config is a fully managed service that provides you with an AWS resource inventory, configuration history, and configuration change notifications to enable security and governance.
With AWS Config you can discover existing AWS resources, export a complete inventory of your AWS resources with all configuration details, and determine how a resource was configured at any point in time.
These capabilities enable compliance auditing, security analysis, resource change tracking, and troubleshooting.
Allow you to assess, audit and evaluate configurations of your AWS resources.
Very useful for Configuration Management as part of an ITIL program.
Creates a baseline of various configuration settings and files and can then track variations against that baseline.
5. AWS CloudTrail
AWS CloudTrail is an application program interface (API) call-recording and log-monitoring Web service offered by Amazon Web Services (AWS).
AWS CloudTrail allows AWS customers to record API calls, sending log files to Amazon S3 buckets for storage. The service provides API activity data including the identity of an API caller, the time of an API call, the source of the IP address of an API caller, the request parameters and the response elements returned by the AWS service.
CloudTrail can be configured to publish a notification for each log file delivered, allowing users to take action upon log file delivery — a process that according to AWS should only take about 15 minutes. It can also be configured to aggregate log files across multiple accounts so that log files are delivered to a single S3 bucket.
The service can facilitate regulatory compliance reporting for organizations that use AWS and need to track the API calls for one or more AWS account. CloudTrail can also be configured to support security information (SIEM) and event management platforms and and resource management.
6. Security Hub
AWS Security Hub combines information from all the above services in a central, unified view. It collects data from all security services from multiple AWS accounts and regions, making it easier to get a complete view of your AWS security posture. In addition, Security Hub supports collecting data from third-party security products. Security Hub is essential to providing your security team with all the information they may need.
A key feature of Security Hub is its support for industry recognized security standards including the CIS AWS Foundations Benchmark and Payment Card Industry Data Security Standard (PCI DSS).
Combine Security Hub with AWS Organizations for the simplest way to get a comprehensive security overview of all your AWS accounts.
Now that we have addressed the top account security tools, let’s focus on the top four AWS application sSecurity tTools you should consider.
Top 4 AWS Application Security Tools
1. Amazon Inspector
Amazon Inspector is an AWS software tool that automatically assesses a customer’s AWS cloud deployment for security vulnerabilities and deficiencies. Amazon Inspector evaluates cloud applications for weak points or deviations from best practices before and after they are deployed, validating that proper security measures are in place. The service then provides and prioritizes a list of security findings, including detailed descriptions of issues and recommendations to fix problems.
Amazon Inspector is available through the AWS Management Console and is installed as an agent on the operating system of Elastic Compute Cloud instances. Amazon Inspector requires an AWS Identity and Access Management (IAM) role, which grants the service permission to itemize instances as well as tags to assess before evaluating the security of a cloud deployment. The service can create an AWS IAM role, if needed.
An IT administrator defines an assessment template, which includes the rules packages to follow, the duration of the assessment run, the topics that result in notifications from Amazon Simple Notification Service and other attributes. The analysis of the target environment is called the assessment run, which analyzes behavioral data within a target, including network traffic on running processes and communication between cloud services.
Amazon Inspector pulls best practices from a knowledge base consisting of hundreds of rules (individual security practices or tests) that are updated by AWS security researchers. Amazon Inspector provides public-facing APIs that allow a user to incorporate the service on non-cloud technologies, such as email or security dashboards.
Amazon Inspector is billed based on the number of assessment runs and systems assessed, combining those elements into a metric called agent-assessments. Amazon provides a free trial before billing a customer per agent-assessment.
2. AWS Shield
AWS Shield protects AWS components against DDoS attacks. These attacks produce huge numbers of artificially generated requests to disrupt public applications. Shield is available in two presentations: Standard and Advanced.
AWS Shield Standard is enabled by default in CloudFront và Route 53 at no extra cost. AWS Shield Advanced is available for those two services plus several others: Elastic Load Balancing, EC2, Elastic IPs and Global Accelerator.
AWS Shield Standard offers protection against certain attacks but lacks flexibility for custom configurations. Shield Advanced integrates with the AWS WAF service to configure specific protection rules. Additionally, Shield Advanced provides access to the AWS Shield response team, a 24/7 support group available for emergencies. It also protects against extra AWS charges that could incur as a result of increased usage due to a DDoS attack; affected customers can request credits.
AWS Shield Advanced costs $3,000 per month. There is an additional data transfer fee, which varies depending on the protected resource type and the amount of data transferred (e.g., <100 TB, 400 TB, 500 TB). The Shield Advanced data transfer fee could be between $25 to $50 for 1 TB of data transferred within the initial 100 TB bracket, depending on the protected resource type. This is in addition to the data transfer fees applicable to each protected resource. The monthly fee is applicable per AWS Organization. Therefore, deployments across multiple AWS accounts within one Organization would pay only a single fee.
3. AWS Web Application Firewall
4. AWS Secrets Manager
AWS Secrets Manager helps you store and protect your secrets needed to access other applications. The service enables you to easily rotate, manage, and retrieve database credentials, API keys, and other secrets throughout their lifecycle.
Instead of hardcoding credentials in your apps, you can make calls to Secrets Manager to retrieve your credentials whenever needed.
With Secrets Manager, you can manage access to secrets using IAM policies and resource-based policies. For example, you can create a policy that enables developers to retrieve certain secrets only when they are used for the development environment.
Automatically rotate your secrets
You can configure Secrets Manager to automatically rotate with an AWS Lambda function. This function defines how Secrets Manager performs the following tasks:
- Creates a new version of the secret.
- Stores the secret in Secrets Manager.
- Configures the protected service to use the new version.
- Verifies the new version.
- Marks the new version as production ready.
Natively supports RDS
Secrets Manager natively supports the following Amazon RDS:
- Amazon Aurora on Amazon RDS.
- MySQL on Amazon RDS.
- PostgreSQL on Amazon RDS.
- Oracle on Amazon RDS.
- MariaDB on Amazon RDS.
- Microsoft SQL Server on Amazon RDS.
Secrets Manager Quotas
You can store a maximum of 500,000 secrets per Region.
The maximum version of a secret is ~100.
The maximum length of a secret is 65,536 bytes.
The length of a resource-based policy (JSON text) is 20,480 characters.
SSM Parameter Store vs Secrets Manager
Secrets Manager:
- More cost.
- Automatic rotation of secrets with AWS Lambda.
- Lambda function is provided for RDS, Redshift, DocumentDB.
- KMS encryption is mandatory.
SSM Parameter Store:
- Less cost.
- Simple API.
- No secret rotation (can enable rotation using Lambda triggered by CW Events).
- KMS encryption is optional.
Kết luận
AWS has an abundance of security services, making it a challenge to pick the right one for your specific needs. If you’re looking for solutions to specific security use cases, it’s worth diving into AWS’ cloud security learning resources.
Identifying vulnerabilities is only a portion of AWS security. Work with Mission to ensure your cloud assets are properly configured from the start. Enabling these tools will provide valuable insight into your AWS account and application security, but the majority of security incidents stem from misconfiguration. Mission can help you choose the right tools to secure your cloud environment.
2022 sparked the AI revolution, 2023 saw it infiltrate the business world, and now, in 2024, we’re at the…

Hey there! Ever wondered what the buzz around MLOps is all about? Let’s break it down! MLOps, short for Machine…

Whisper represents a cutting-edge neural network model meticulously crafted by OpenAI, designed to adeptly tackle the complexities of speech-to-text conversions.…

Software development costs can be assessed through various methodologies, with two prominent approaches standing out: calculating based on module or…
Low-Code/No-Code (LCNC) Application Development: Revolutionizing Business Solutions In the realm of application development, businesses traditionally faced two options: purchasing pre-made…

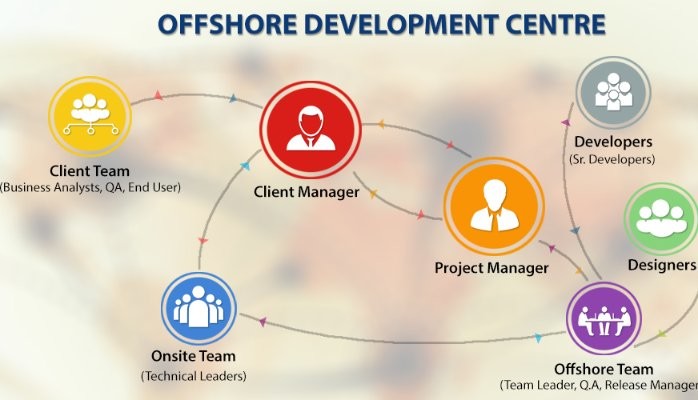
Are you facing challenges in finding the ideal software development partner for your project? The abundance of options can make…

Outsourcing software development has emerged as a cost-effective solution for numerous businesses, allowing them to optimize expenses without compromising project…
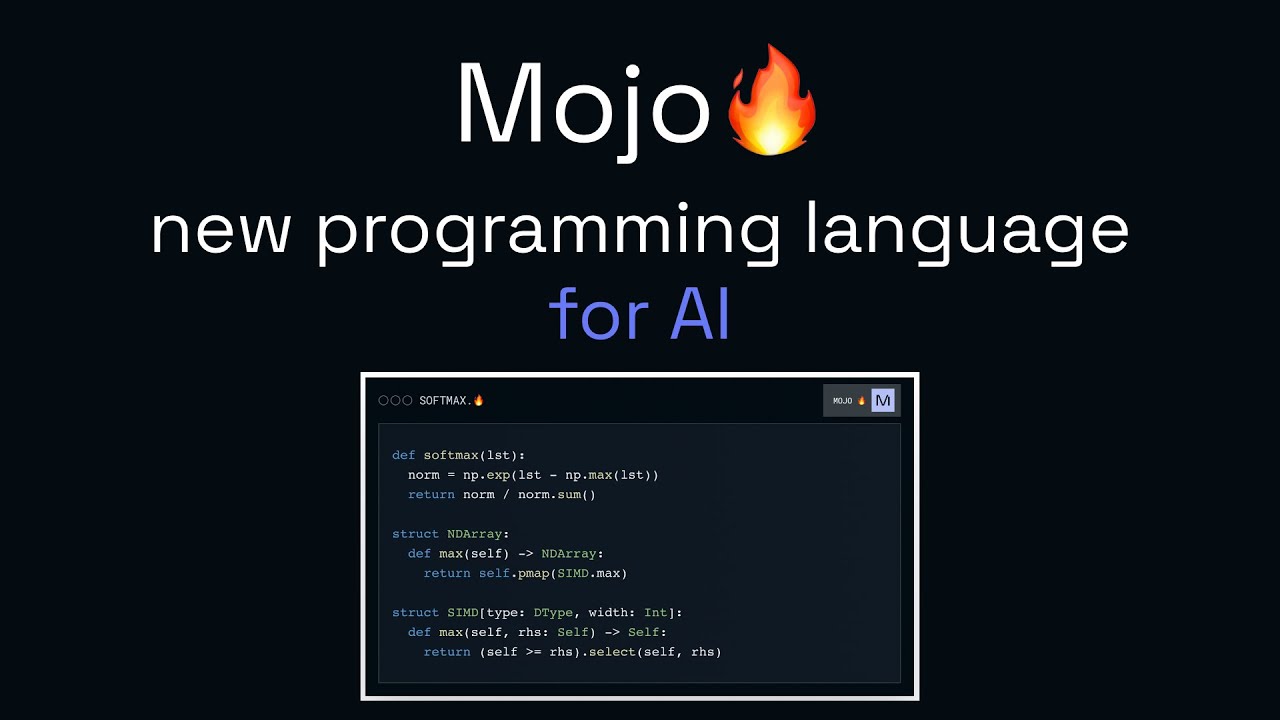
Mojo is a sophisticated predictive modeling technology developed by H2O.ai, the company renowned for its popular open-source machine learning platform,…
The emergence of remote work has ushered in a transformative employment landscape. A global phenomenon, millions of individuals worldwide have…

Determining the cost of software development is an essential preliminary step prior to embarking on its construction. It is imperative…
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Hi there, thanks for reading our blog posts. I am always happy to answer any questions you have about the article.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Hi there, thanks for reading our blog posts. I am always happy to answer any questions you have about the article.
After reading your article, I have some doubts about gate.io. I don’t know if you’re free? I would like to consult with you. thank you.
Thank you for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
I may need your help. I tried many ways but couldn’t solve it, but after reading your article, I think you have a way to help me. I’m looking forward for your reply. Thanks.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
Reading your article helped me a lot and I agree with you. But I still have some doubts, can you clarify for me? I’ll keep an eye out for your answers.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
I was recommended this web site by my cousin. I’m not sure whether this post is
written by him as nobody else know such detailed about my problem.
You’re amazing! Thanks!
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
hey there and thank you for your information – I
have definitely picked up anything new from right here.
I did however expertise several technical issues using this website, as I experienced to reload the site lots of times previous to I could get it to load correctly.
I had been wondering if your web hosting is OK? Not that I’m complaining, but slow loading
instances times will sometimes affect your placement in google and can damage your
high-quality score if advertising and marketing with Adwords.
Anyway I am adding this RSS to my e-mail and can look out for much more of your respective intriguing content.
Ensure that you update this again very soon.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
I am regular visitor, how are you everybody? This piece of writing
posted at this website is really good.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
Heya i’m for the primary time here. I came across this board and I to find It really helpful & it helped me out much.
I’m hoping to offer one thing back and aid others
such as you helped me.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
Wonderful article! We are linking to this great post on our
website. Keep up the good writing.
Thank you very much for sharing, I learned a lot from your article. Very cool. Thanks. nimabi
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap.
Now all became clear, many thanks for an explanation.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
My family every time say that I am killing my time here at web,
except I know I am getting knowledge daily by reading thes fastidious content.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
Hi! I know this is kind of off topic but I was wondering which blog
platform are you using for this website? I’m getting tired of WordPress because
I’ve had issues with hackers and I’m looking at options
for another platform. I would be fantastic if you could point me in the direction of a good platform.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
hello!,I like your writing so so much! percentage
we be in contact more about your article on AOL? I require a specialist on this space to resolve my problem.
May be that’s you! Looking forward to see you.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thanks for paying attention to our blog. Our consultation is free so you can leave your questions here and we will try to answer them asap